Managed services are one way for accounting firms to ensure their information technology is secure. We put together this article and podcast to help accounting firms make the right decisions when it comes to their managed services. At the end of the day, it’s about doing what’s right, and to follow data-security laws.
What are managed services?
Managed services is the decision for accounting firms – usually small to mid-size – to outsource their IT support. Instead of hiring somebody full-time to work in the office they hire an outside tech support firm that handles all their needs – usually remote. Remote managed services technicians can easily and quickly dial into your computer or network to address issues.
[Tweet “Hiring an outside firm for tech support can be valuable if the firm is knowledgeable.”]
Managed services firms also keep an eye on the pulse of changes in the industry, laws and others security updates that need to be implemented.
What are some recent security changes to be aware of?
As Andrew Lassise mentioned on the podcast, IRS Publication 4557 was one such update that impacted accounting firm compliance with the law and good information security. The publication highlights six areas that help you keep your data more secure. A good managed services firm can help you keep those six areas up to date.

Anti-virus protection
Active anti-virus protection is a must for all computers on your network. Despite what some so-called experts have said, you don’t need more than one anti-virus program running.
“You are not doubling the protection by adding another program,” said Andrew.
It’s important that you have a secure and up to date antivirus program in place to catch malware.
Malware can infect computers which are operated by even the most savvy of users. It’s usually downloaded by mistake.
That’s why it’s necessary to have an antivirus software which receives regular updates and can scan for the latest threats without you ever prompting it to.
Your managed services firm would handle those updates for you automatically.
[Tweet “Antivirus should stop a threat in its tracks as soon as possible.”]
When it comes to free services, they often give users an option. A notification pops up that a potential problem exists and the user can decide from there:
- Run program anyway
- Do not run it
“The user gets to decide well, I’ll infect it anyway,” Andrew said.
When you use managed services antivirus it’s says: “I think this is a virus. Call the tech if you think this should be led through.”
Then you have experts that are looking at it.
[Tweet “Just one bad email can wipe out the entire company network.”]
Having the right managed services protections in place will take that decision point out of the individual user’s hands and puts it into the hands of your managed services provider.
Need help with your managed services? Contact us by filling out the form
Working firewall
A firewall and antivirus program are not the same thing. A firewall is more about who has access and how they have access. A firewall protects access.
Two-factor authentication
A lot of people don’t like it because it adds a step into logging into their account. But it also helps with security.
How does two-factor authentication work? Traditionally, you’d type in your password and you are in. With two-factor authentication, you’ll type in your password and then get a notification on a device – like your phone – that you carry with you. Once you enter your password a code will be send to your device to verify it’s really you. This is a great safety measure when passwords are stolen.
[Tweet “Two-factor authentication can save your company when passwords were stolen.”]
“Humans like the path of least resistance,” Andrew said. “A lot of people use the same password for everything.” With two-factor authentication, at least it’s an added security layer when people do that. Your managed services firm can set 2FA up for you.
“That way even if somebody unauthorized has your password you are still protected,” Andrew explained.
Working backup
Backing up your files into the cloud is an important way to ensure your data is protected. Live Drive, for example, backs up your data whenever a file modification is made.
Think of backups as your parachute. Let’s say somebody clicks on a bad link in which a computer was infected and a ransomware attack just happened.
What is a Ransomware attack? In a ransomware attack, hackers access your files and basically lock them away from you. You can’t access them. They will then ask you to pay a ransom to get the files back. Even if you pay, that doesn’t mean they will release the files back to you.
In this case, the damage has been done. Calling the fire department after the house has burned to the ground won’t save the house.
“The damage has been done,” Andrew said. “If you have back up that’s your restart button. You can put it back to how it was before the infection happened.”
Of course, the backup has to be set up correctly, which a good managed services firm can easily help you with. We recommend cloud backup.
What is Cloud Backup?
Cloud storage is similar to backing up your files traditionally to an external drive. The difference is that the external drive is offsite and maintained by a company which specializes in cloud backup.
Drive encryption
In a ransomware attack, hackers encrypt your files and basically lock them away from you. You can also use encryption to keep files away from hackers. If files are encrypted and intercepted or accessed by an unauthorized person they can’t see the content.
“Somebody steals a return from 2000 that’s on your computer, that information is enough to open credit cards or take out lines of credits,” Andrew said. “They can commit identify theft with that information. It falls on the accountants to protect that information.
Need more information on how to encrypt your data? Contact us now.
Use of VPN
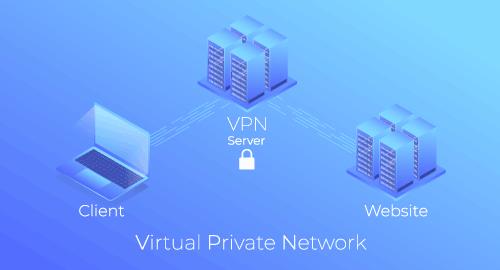
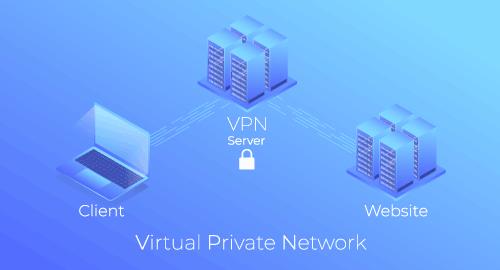
In the end, you see the data the same as if you were surfing on the web. It does take a little longer, as you are running a network within a network. Also, if the server is very busy with too many users, the experience can be much slower. Many VPN providers will show you in advance how active a particular IP address connection is before you connect to help alleviate slower connections.
Public Wi-Fi
Andrew also recommends to never connect to a public Wi-Fi while conducting any sensitive business. Agents in the field will tell you sometimes that seems impossible to do. You can eliminate concerns about connecting to a public Wi-Fi with a VPN Hotspot. A VPN can help secure an open connection, making it encrypted and out of bounds for hackers. Using a VPN also provides anonymity when surfing the web. If you are tracking your competition and watching what they are doing on their website, today, they may be watching you do that as they can capture your IP address. With a VPN, you are a ghost, as your IP address stays hidden. None of your actions are traceable to you, as you are browsing the web anonymously with a VPN. You are leaving no online browsing footprint.
What a VPN can offer an agent concerning security protection is greater peace of mind. Finally, many large brokerages, like all mortgage companies, use a VPN to allow their employees to connect back to their office network. This is far more secure than through a hackable internet network.
Managed IT services can keep your computer and network running in tip-top shape. For example, we use an RMM (Remote Management and Monitoring) software called Syncro to automate your security and take it of your to-do list.
Information on the status of your computer is sent in real-time and possible issues are stopped before they even happen. In addition to what we shared above you should also expect the following from your managed services partner:
Professional Help
Great managed services firms are quick, professional and help you stay secure by using their vast knowledge.
Accessibility
Speed matters, which is why it’s a best practice in managed services to have technicians available to respond to customer needs and questions.
An On-Call IT Department
Skilled computer technicians are highly sought after. The best IT professionals have gone to school for several years, paid for multiple costly certifications, and have years of experience. Employing one skilled technician is easily upwards of $45,000/year. Factor in benefits, 401k, vacation days, etc. and the cost is even higher let alone hiring two or more qualified technicians to cover your business hours or workload.
When you hire a properly staffed IT company their availability is much more extensive. These Managed Service Provider IT companies provide much better coverage than the one or two employees could ever hope for.
Protected Personal Information
Your client or personal information has value to hackers and those interested in committing identity theft. Protecting this information should be one of your top priorities. If you make IT security an afterthought than it’s already a problem. Your possible issues for not securing that information can be substantial. That’s if you can afford to pay for it. Purchasing managed IT services are the better and cheaper option in the long run.
Proactive Protection
Cyber threats are always evolving and changing. Even as old exploits are patched or repaired new exploits are found and then taken advantage of. Even being a few months behind the curve with cyber-security could mean that private information is vulnerable. Almost everyday news comes out about the latest threats and how to prevent them. Who has time to keep up with that flood of information? Companies whose job it is to protect their clients and have years of expertise doing just that.
